1. Introduction to AES Encryption
AES (Advanced Encryption Standard) is a symmetric encryption algorithm, which means that the same key is used for both encryption and decryption. It is widely used for data encryption and information security protection. It was officially published by the National Institute of Standards and Technology (NIST) in 2001, replacing the previous DES (Data Encryption Standard).
2. Classification of AES
| Name | AES-128 | AES-196 | AES-256 |
| Plaintext Block Length / bits | 128 | 128 | 128 |
| Key Length / bits | 128 | 196 | 256 |
| Number of Rounds | 10 | 12 | 14 |
-
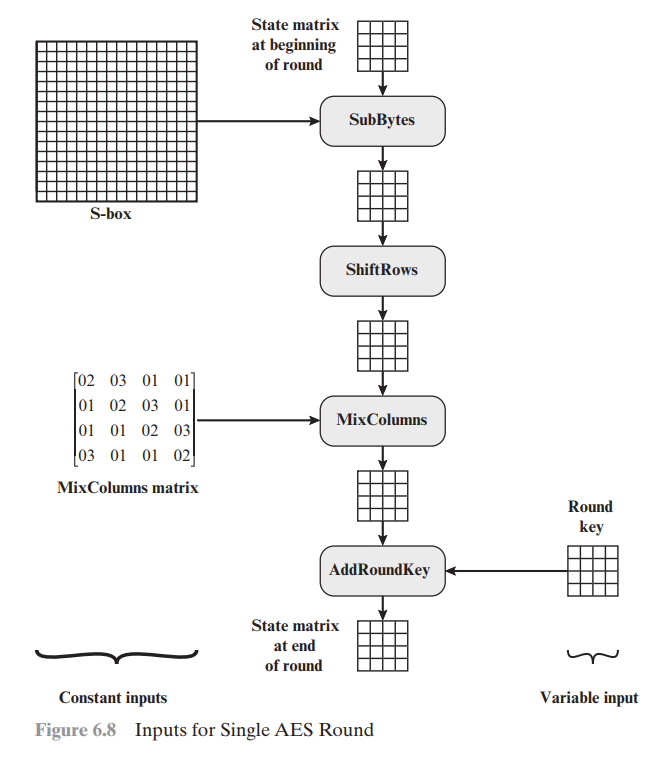
Plaintext block — 128 bits. The input to the encryption and decryption algorithm is a 128-bit block. These blocks are represented as a 4×4 byte matrix, which is copied into a 16-byte array and modified at each stage of encryption and decryption.
-
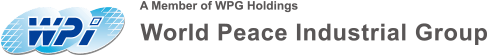
Key expansion — w[0, 3] to w[40, 43], which will be represented as k0 to k10, a total of 11 ks. The specific steps of key expansion will be described in Chapter 6.
-
Initial transformation of the 0th round iteration — Plaintext ⊕ K0.
-
9 rounds of iteration, each round includes 4 steps — Byte substitution, row shifting, column mixing, and round key addition.
-
The 10th round iteration, only 3 steps — Byte substitution, row transformation, and round key addition.
-
Ciphertext block — 128 bits.
-
Ciphertext ⊕ K10 (corresponding to the initial transformation).
-
9 rounds of iteration — Inverse row shifting, inverse byte substitution, round key addition, inverse column mixing.
-
Iteration 10 —— Inverse Shift Rows, Inverse Byte Substitution, Add Round Key.
-
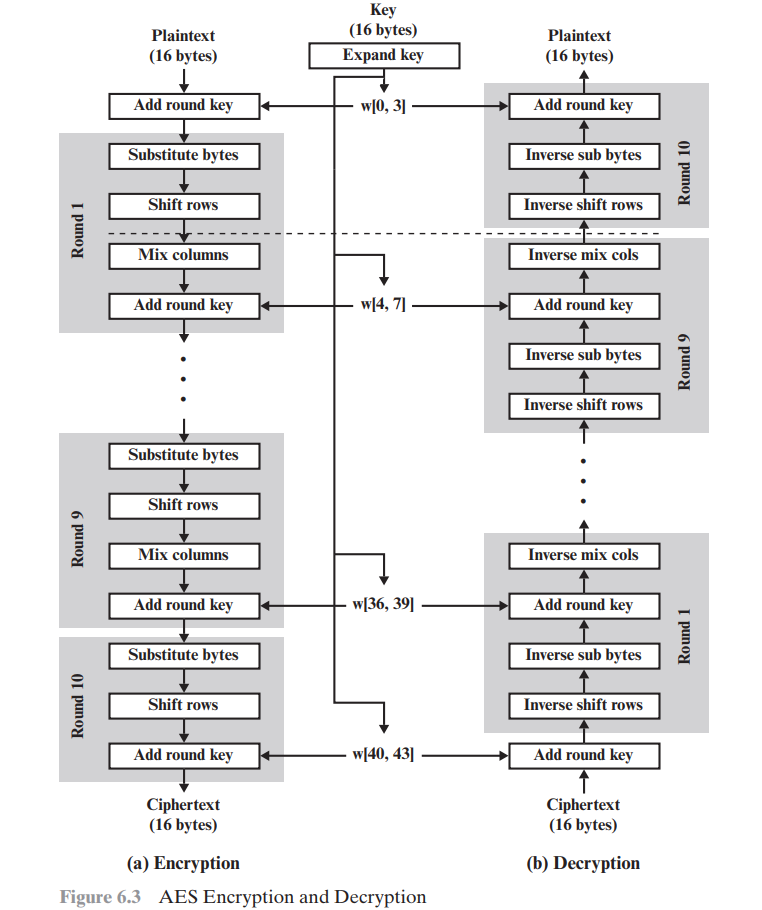
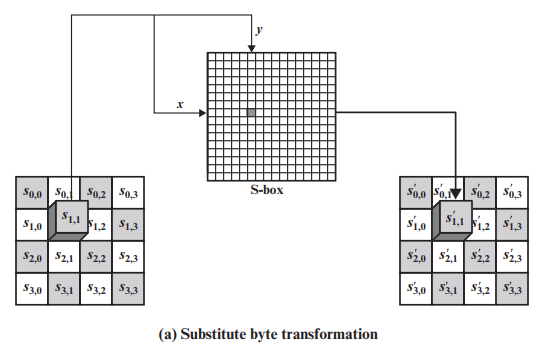
Byte Substitution
-
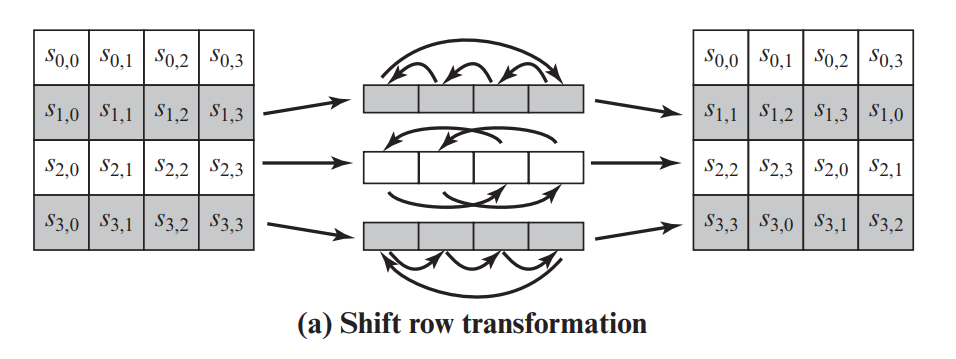
Shift Rows
Inverse Transformation:
-
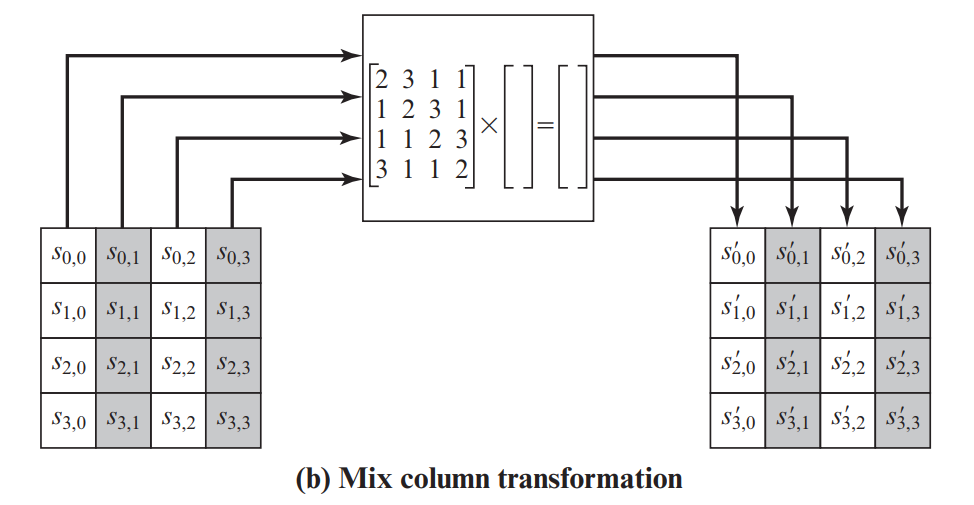
Column Mixing
-
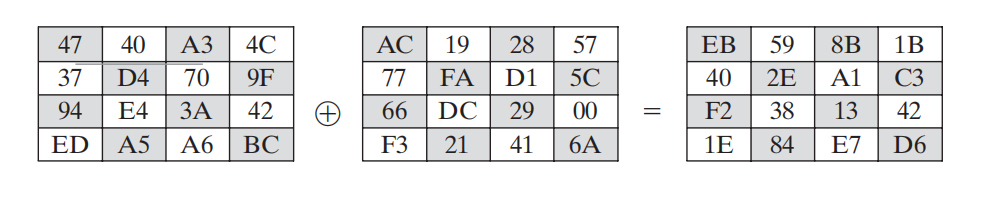
Add Round Key
-
This stage is the only step in encryption/decryption that involves the key.
-
Initialization: Construct a 16*16 S-box. Set the initial value at position (y, x) to {yx}.
-
Find the inverse of {yx} in GF(2^8). 【For finding the inverse, refer to: Euclidean algorithm, Extended Euclidean algorithm (Euclid), and how to find the inverse of AES's S-BOX - CSDN Blog】
-
Transform the result matrix from step 2 (invertible).
-
Convert the column vector (binary number) to bytes (hexadecimal number) and fill it into (y, x).
-
Take input {95}
-
The inverse of {95} is {8A}={10001010}
-
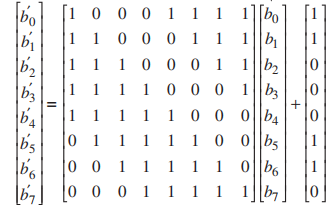
M * [0 1 0 1 0 0 0 1](T) + [1 1 0 0 0 1 1 0](T)
-
The result converted to hexadecimal equals {2A}
-
Convert the byte to a column vector
-
XOR the result from step 1 and apply the inverse matrix transformation
-
Convert the column vector back to a byte
-
Find the inverse of {yx} in GF(2^8)
-
Fill in the corresponding position in the inverse S-box
-
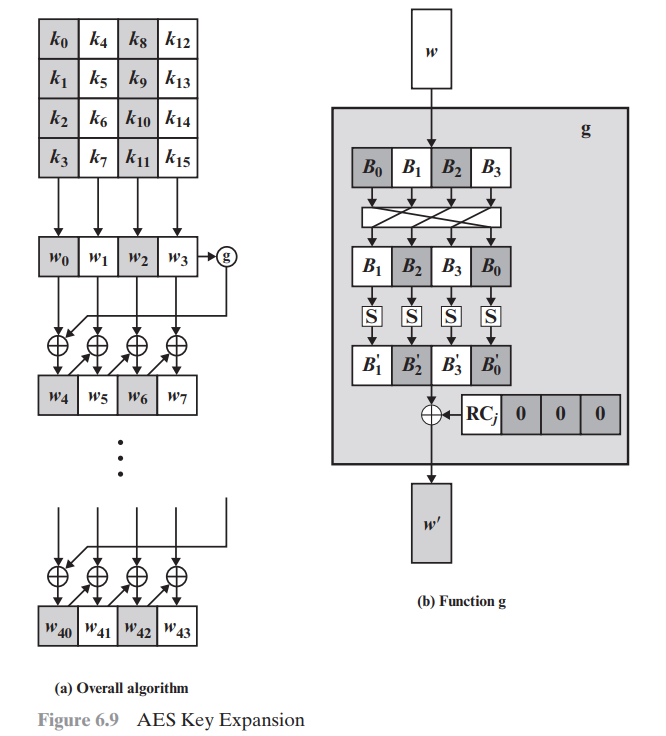
AES-128 uses a 10-round encryption process. Each round requires a round key.
-
In addition to these 10 rounds, there is an initial round where the original key is used. Therefore, a total of 11 round keys are needed.
-
The input key is directly copied to W0 to W3.
-
The last W of each row, such as W3, is processed through the g function to become W '.
-
W4n = W ’ ⊕ W4n-4, [ n = 1,2,3…10 ], (the first W of each row).
-
Wm = Wm-1 ⊕ Wm-4, [ m ≠ 4n ], XOR the above with the left, (the last three W of each row).
-
Repeat steps 3 and 4 until W43 is computed. [ Because 44/4 = 11 groups of subkeys ] [11 = 1+9+1]
-
Output.
-
B is cyclically left-shifted by one position.
-
Each of the four B's is replaced using the S-box. (Same as the S-box in the first stage of encryption byte substitution)
-
XOR with the round constant Rcon[ j ]. (To eliminate symmetry)
-
Output.
-
"Cryptography and Network Security Principles and Practice"